How to connect your home systems to a VPN on AWS in under 30 mins : Home Lab — Part 2
In this part I am going to create an EC2 instance, setup openvpn on it and connect all nodes at my home to the VPN. You can read the previous part here
Last week I started working on building a home lab in which I can run containers and non critical workloads. I am already stuck with deciding if I should use docker-swarm or consider kubernetes. In last few days I’ve come across some brilliant tools to like k8s and microk8 to run lightweight kubernetes cluster and that has made me think. I have still not made a decision because it’s a tough one. Although the important bit is to build the infra so I decided to first get all the connections done first and worry about the orchestration framework later.
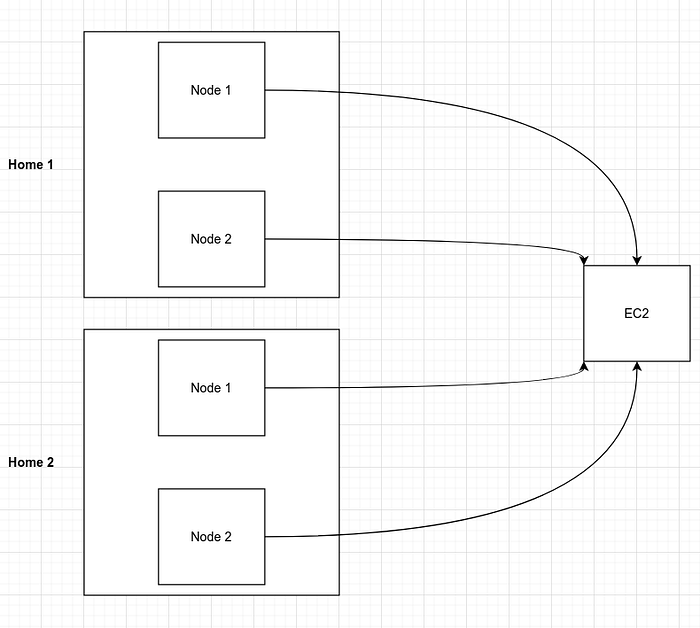
Basic architecture
So to build out my home lab I will have one node on AWS which will always be alive (hopefully) and I’ll use it for serving traffic which might require high uptime. Other nodes will be sitting inside my home and possibly in other people’s home who would be generous enough to join my cluster. :D Below is a picture of how the connections will look like. All nodes running at different places behind firewalls or NAT will connect to the VPN running on EC2 instance and that’s how they will communicate with each other.
Create an EC2 Instance
You can do this in multiple ways. For me I have a terraform template which creates EC2 instance with configuration that I want. If you are a beginner I would highly recommend this terraform module, it will save a lot of your time. You can create the instance from console , CDK, aws cli or any other method which suits you as long as the following requirements are met by the instance
- 1 GB Ram and 1 vCPU
- At least 20GB storage
- Public IP
- Ubuntu AMI (You can use any other linux AMI but to follow along ubuntu would help)
Setup VPN on EC2 Instance
I used this github repo to setup a VPN in 5 mins : https://github.com/angristan/openvpn-install
Important bit to note here is that the defaults provided by the installer script work seamlessly with AWS so you can get the VPN server up and running only in a few minutes without breaking your head over things.
Once the setup is complete and ovpn file is generated just double check if all is well:
ubuntu@ip-10-1-22-109:~$ ifconfig tun0
tun0: flags=4305<UP,POINTOPOINT,RUNNING,NOARP,MULTICAST> mtu 1500
inet 10.8.0.1 netmask 255.255.255.0 destination 10.8.0.1
inet6 fe80::da79:ab62:946f:51b0 prefixlen 64 scopeid
.....
.....Connect all nodes to VPN
Creation of cert for each node is fairly straightforward. Every time I need to add a new node I can use the script from the above github repo and things just work like a charm!
ubuntu@ip-10-1-22-109:~$ sudo ./openvpn-install.sh
Welcome to OpenVPN-install!
The git repository is available at: https://github.com/angristan/openvpn-installIt looks like OpenVPN is already installed.What do you want to do?
1) Add a new user
2) Revoke existing user
3) Remove OpenVPN
4) Exit
Select an option [1-4]: 1Tell me a name for the client.
The name must consist of alphanumeric character. It may also include an underscore or a dash.
Client name: node1Do you want to protect the configuration file with a password?
(e.g. encrypt the private key with a password)
1) Add a passwordless client
2) Use a password for the client
Select an option [1-2]: 1# At the end you should have a node1.ovpn file at your home directory
ubuntu@ip-10-1-22-109:~$ ls -lrth node1.ovpn
-rw-r--r-- 1 root root 2.8K May 22 19:35 node1.ovpn
Now, to connect the first node at my home which has a fresh ubuntu installation this is all that I had to do
# Install openvpn clinet
sudo apt install openvpn# Create a new file with name myvpn.conf and copy contents of node1.ovpn into it sudo cp mypvn.conf /etc/openvpn/
sudo systemctl enable openvpn@myvpn
sudo systemctl start openvpn@myvpn
Using systemd ensures that the vpn connects on boot and also reconnects by itself in case of intermittent network failures. I have configured openvpn client with systemd on multiple devices and I have found it to be extremely reliable.
Now to confirm connectivity
# Ensure VPN is UP
vikas@home-pc ~ ❯❯❯ sudo systemctl status openvpn@mypvpn
● openvpn@myvpn.service - OpenVPN connection to myvpn
Loaded: loaded (/lib/systemd/system/openvpn@.service; indirect; vendor preset: ena
Active: active (running) since Sat 2021-05-08 01:03:40 IST; 2 weeks 1 days ago
Docs: man:openvpn(8)# Ensure you are able to ping the vpn server. 10.8.0.1 is the IP of your EC2 instance on the VPN
vikas@home-pc ~ ❯❯❯ ping 10.8.0.1
PING 10.8.0.1 (10.8.0.1) 56(84) bytes of data.
64 bytes from 10.8.0.1: icmp_seq=1 ttl=64 time=34.9 ms
64 bytes from 10.8.0.1: icmp_seq=2 ttl=64 time=34.8 ms
64 bytes from 10.8.0.1: icmp_seq=3 ttl=64 time=34.8 ms
^C
--- 10.8.0.1 ping statistics ---
3 packets transmitted, 3 received, 0% packet loss, time 2001ms
rtt min/avg/max/mdev = 34.825/34.878/34.920/0.039 ms
And that’s it. My first node is connected to the VPN. It was a no-brainer to repeat the same process for the other node and in less than 30 mins I had all my spare servers connected to the VPN.
In the next articles in this series I’ll discuss setting up a production ready container orchestration platform above this cluster. A detailed roadmap of my plan is available here.
